Cloud
Cloud

When the "Cloud" option is enabled, the application can copy the collected logs to an external cloud database, which can also be accessed externally through the web portal http://cloud.businesslog.it.
The connection can be tested usting the [Test] button.
ATTENTION:
To use cloud storage, you must open TCP port 1433 in your firewall (if present).
Azure

Using the "Azue" plugin, it is it is possible to record access logs for Azure accounts.
To enable log collection on the platform side, the application must be registered and its access authorised.
1. Log in to the Azure Portal (portal.azure.com) and click on Azure Active Directory.

2. From the menu on the left click: "App registrations".

3. From the top menu click: "New registration".

4. When ready, click [Record]. The configuration page of the newly created application will be displayed.
5. From the menu on the left now click: "New Client Secret".
The following information is displayed (on the right):


6. Click "New Client Secret". The following information is displayed (on the right):

7. Enter a name and save it.
8. From the menu on the left, click "Api permissions".


9. Click "Add a permission". The following information is displayed (on the right):

10. Select Microsoft Graph

11. Choose"Application permissions".
12. In the search box, enter "auditlog" the available permission are displayed:

13. Finally, click su “Add permissions”.
ATTENTION:
To allow emails to be sent through an Office 365 account, the Mail.Send permission must also be added. If the Azure plugin is not used, it is sufficient to authorise email permissions only.
Your permissions should now appear as follows:

14. Now click on “Grant admin consent for …”.
ATTENTION:
You mus be an administrator to grant this permission.
15. In the “Overview” section from the menu on the left, note the Application (client) ID and the Directory (tenant) ID.


16. In the "Certificates and secrets" section you can access the ClientSecret value.

17. Copy the value from the "Value" column (using the dedicated icon).
ATTENTION:
The copy of the "Client Secret Value" is only possible immediately after creation.
18. Complete the configuration and perform the tests before closing the window. Otherwise, the certificate needs to be regenerated.
19. In BusinessLog go to Setting > Cloud. The following information will be displayed:

In this table, you can specify one or more Microsoft Azure tenants to access. By pressing [Ab], you can edit the rows:
The configuration can be verified by clicking [Test].
ATTENTION:
Tenant access authorisation expires every X months and must be renewed manually through the Azure portal. The expiration date is defined at the time the certificate is generated.
-
Use Mail Account flag
Allows the tenant to be specified as the sender account for the selected mailbox.
When logs are acquired from SharePoint or OneDrive, the following options must also be enabled:

It is recommended to create a new permission, which results in a new Client ID and Client Secret, with the following entries enabled for the Microsoft O365 APIs:
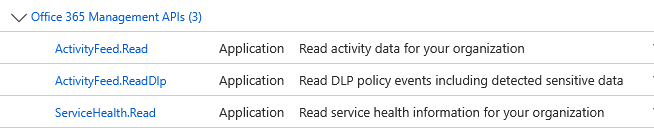
In the Azure table add: